Here you set the encryption profile for each SSID. The following encryption profiles are stored by default and these can be used for the configuration of the WLAN networks.
- P-NONE
- No encryption, the SSID is open.
- P-PSK-WPA2
- The authentication method used is WPA2 with pre-shared key (PSK), also known as WPA2-Personal. A key must be configured for the WLAN network.
- P-PSK-WPA2-3
- The authentication method used is WPA2 and/or WPA3 with pre-shared key (PSK), also known as WPA-Personal. A key must be configured for the WLAN network.
- P-PSK-WPA3
- The authentication method used is WPA3 with pre-shared key (PSK), also known as WPA3-Personal. A key must be configured for the WLAN network.
- P-PSK-WiFi7
-
Ccertain encryption settings are mandatory for standards-compliant Wi‑Fi 7 and Multi Link Operation:
- The WPA session key type must include AES-GCMP-256
- The Group Mgmt Cipher must be BIP-GMAC-256
- The SAE/OWE-DH groups must include DH-19, DH-20, and DH-21
- Protected Management Frames (IEEE 802.11w) must be enabled
- Beacon Protection must be enabled

- Profile-Name
- Choose a meaningful name for the encryption profile here. This internal identifier is used to reference the encryption profile from other parts of the configuration.
- Select authentication
-
Change the encryption and authentication method here. WPA2-PSK (WPA2 with pre-shared key or WPA2-Personal) is preset by default. Optionally select No encryption or one of the following options:
- WPA3-PSK – WPA3 with pre-shared key or WPA3-Personal
- WPA(2+3)-PSK – WPA2 and/or WPA3 with pre-shared key
- WPA2-801.1X– WPA2 with 802.1X or WPA2-Enterprise
- WPA3-801.1X– WPA3 with 802.1X or WPA3-Enterprise
- WPA(2+3)-801.1X– WPA2 and/or WPA3 with 802.1X
Note:When using methods requiring a pre-shared key (PSK), you need to enter a WPA key. You can read the key by clicking on the crossed-out eye symbol. Depending on your needs, you can automatically generate a secure WPA key (
 ).Note:
).Note:In the case of 802.1X you have to create a RADIUS profile. To do this, click on Edit RADIUS profile and add a new line there.
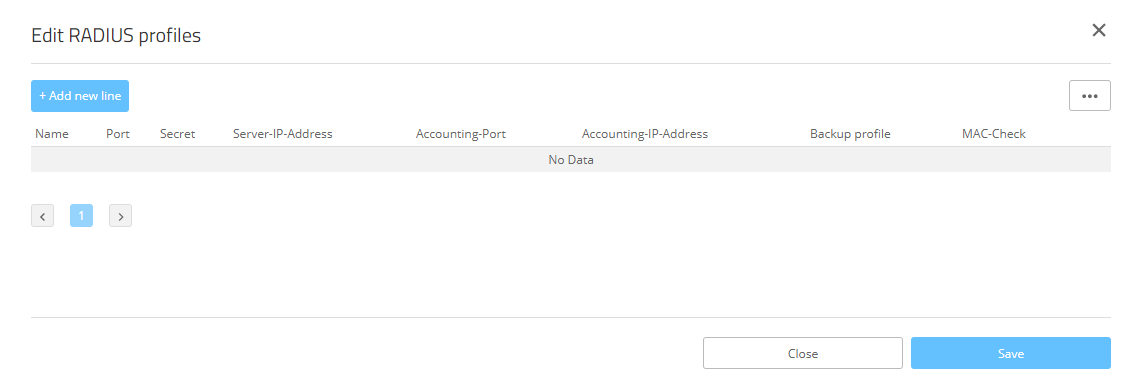
- Name
- Choose a meaningful name for the RADIUS server profile here. This internal identifier is used to reference the RADIUS server profile from other parts of the configuration.
- Port
-
Select the port (UDP) used to contact the RADIUS server.
Note: This is usually the port 1812 (RADIUS authentication).
- Secret
- Here you configure the secret used to encrypt the traffic between the device and the RADIUS server. This secret must also be stored on the RADIUS server.
- Server IP address
- Here you configure the host name or IP address where the RADIUS server is to be reached.
- Accounting port
-
Select the port (UDP) used to contact the RADIUS accounting server.
Note: This is usually the port 1813 (RADIUS accounting).
- Accounting IP address
- Here you configure the host name or IP address where the RADIUS accounting server is to be reached.
- Backup profile
- Here you configure a backup profile, which will be used if the RADIUS server in the profile configured here cannot be reached.
- MAC check
- A user name can be authenticated with a MAC address instead of using the RADIUS server.
Important: Please note that the RADIUS server generally has to be notified about the RADIUS client by means of an entry in its configuration.Store your changes by clicking on Save. - Roaming
-
Settings for switching a client from one access point to another access point that broadcasts the same SSID.
- Standard
- Enables key management according to the IEEE 802.11i standard without Fast Roaming and with keys based on SHA‑1. Depending on the configuration, the WLAN clients in this case must use Opportunistic Key Caching, PMK caching or pre-authentication.
- Fast roaming
-
Enables fast roaming according to the IEEE 802.11r standard. See also Fast roaming.
Note: Fast roaming is possible between devices based on LCOS and LCOS LX.
- Standard+Fast-Roaming
- A combination of standard behavior and Fast Roaming.
Important: Although it is possible to make multiple selections, this is advisable only if you are sure that the clients attempting to login to the access point are compatible. Unsuitable clients may refuse a connection if an option other than Standard is enabled.
- OKC (Opportunistic Key Caching)
- This option enables or disables the opportunistic key caching (OKC). The authentication of WLAN clients via EAP and 802.1X is now standard in company networks, and for public Internet access, too, it is part of the Hotspot 2.0 specification. The disadvantage of authentication via 802.1X is the noticeably longer time between authenticating and connecting due to the exchange of up to twelve data packets between the WLAN client and access point. This may not matter for most applications that only involve exchanging data. However, time-critical applications such as Voice-over-IP rely on fast authentication when moving between WLAN radio cells so as not to impair communications. Various authentication strategies have been established to counteract this, including PMK caching and pre-authentication, although pre-authentication by no means solves all of the problems. For one thing, there is no guarantee that the WLAN client can detect whether the access point is capable of pre-authentication. Also, pre-authentication causes a considerable load on the RADIUS server, because it has to process the authentications of all clients and all access points on the WLAN network. With opportunistic key caching, the management of WLAN client keys is moved to a WLAN controller (WLC) or central switch, which manages all of the access points in the network. When a client authenticates at an access point, the downstream WLC, which acts as the authenticator, performs the key management and returns the PMK to the access point for forwarding to the client. If the client moves to another cell, it uses this PMK and the MAC address of the new access point to calculate a PMKID, and it sends this to the new access point in the expectation that OKC is enabled (i.e. "opportunistic"). If the access point is unable to handle the PMKID, it negotiates a regular 802.1X authentication with the client. A LANCOM access point is even able to perform OKC if the WLC is temporarily unavailable. In this case it stores the PMK and sends it to the WLC, once available again. The WLC then sends the PMK to all of the access points in the network so that the client can continue to use OKC when moving between cells. In networks managed from the LANCOM Management Cloud (LMC) or networks from standalone access points, the PMKs are transmitted via the IAPP protocol. In LMC-managed networks, the IAPP is configured automatically. In networks made up with standalone access points, you have to ensure that the PMK-IAPP secret is configured and identical on every access point in the network.
- IAPP passphrase
- This passphrase is used to implement encrypted Opportunistic Key Caching. This is required to use Fast Roaming over IAPP. Each interface must be assigned an individual IAPP passphrase in the WLAN connection settings. This is used to encrypt the pairwise master keys (PMKs). Access points that share a matching IAPP passphrase (PMK-IAPP secret) are able to exchange PMKs between one another and ensure uninterrupted connections. You should therefore ensure that this passphrase is identical on all of the access points that should operate fast roaming.
- Encrypt management frames
-
By default, the management information transmitted on a WLAN for establishing and operating data connections is unencrypted. Anybody within a WLAN cell can receive this information, even those who are not associated with an access point. Although this does not entail any risk for encrypted data connections, the injection of fake management information could severely disturb the communications within a WLAN cell.
The IEEE 802.11w standard encrypts this management information (protected management frames, PMF), meaning that potential attackers can no longer interfere with the communications if they don’t have the corresponding key.
Note: As of WPA3, management frames have to be encrypted, so the value there is ignored and is assumed to be set as Mandatory. For WPA2, this is optional.
